Protecting IMSI from Fake Base Stations Exploitation and Spoofers Impersonation in 5G and Beyond Cellular Networks.
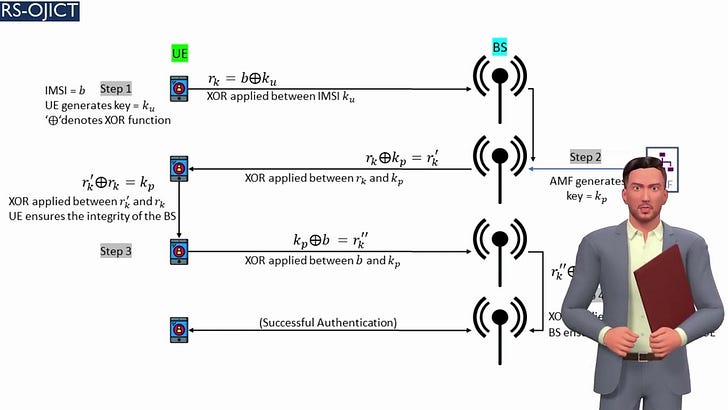
Authors propose a novel hack-proof framework that can perfectly secure IMSI numbers, resulting in having protection against spoofing attacks. The proposed algorithm includes a mobile device (UE) and a gNodeB (BS) that communicate in the clear to authenticate each other securely.
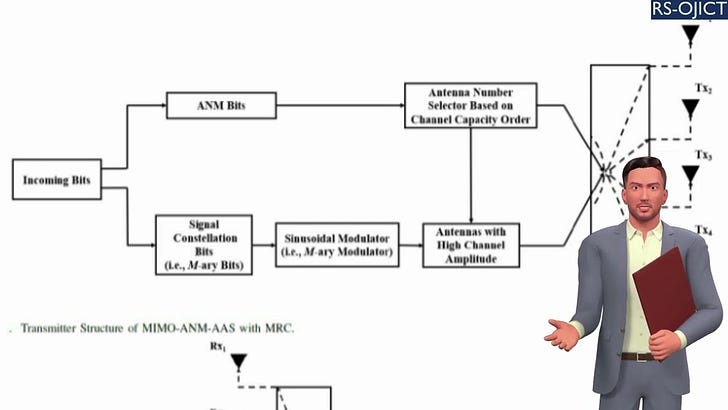
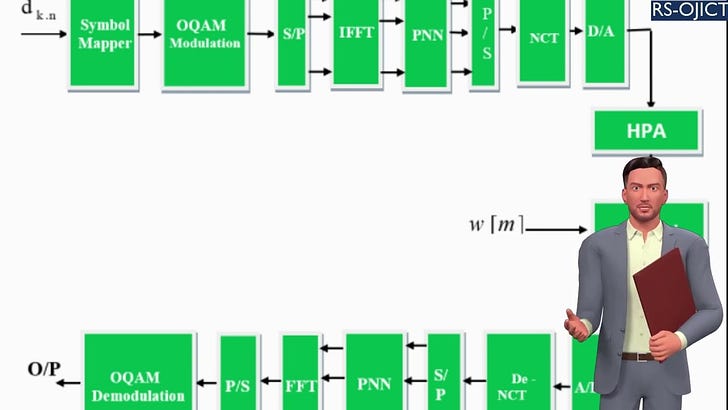
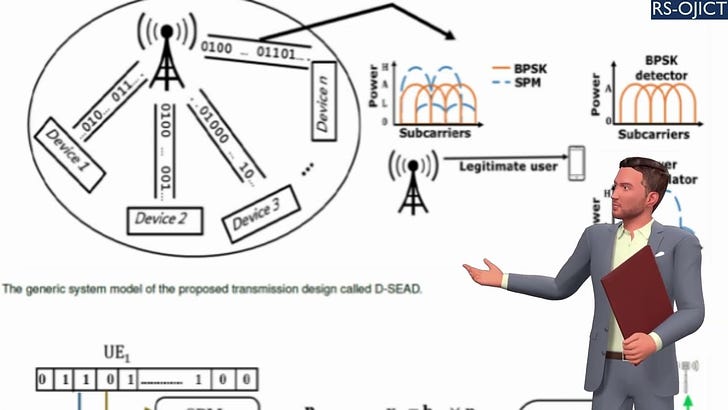
Summary: Fifth-generation (5G) mobile networks require authenticated and fully secured transmissions between user devices and 5G base stations (gNodeB). In the current 5G technology standard, mobile devices cannot distinguish between a real and a fake base station (BS) by following the standard 5G security protocols. This vulnerability is a dangerous security issue identified in 5G cellular networks worldwide, where hackers and spoofers can easily impersonate or hack the valuable information of mobile users. Although 5G security protocols are enhanced to prevent such kinds of attacks, fake BSs still threaten the security of wireless communication networks. To the best of the authors’ knowledge, there is currently no security method available in the literature that can enable users to identify who is sending the connection request response. Thus, this can allow an attacker to intercept the international mobile subscriber identity (IMSI) easily in the clear. Therefore, in this work, we propose a novel hack-proof framework that can perfectly secure IMSI resulting in prevention against spoofing attacks. The proposed algorithm includes a user equipment device (UE) and a BS that communicate in the clear to securely authenticate each other in a TDD fashion. For simulation purposes, an OFDM transmission scheme is considered over a multipath wireless fading channel. The obtained results show that our proposed method works successfully without affecting the reliability of the transmitted bits compared to plain data transmission methods. More specifically, the performance results are shown to be similar to normal OFDM-based data transmission schemes conducted over general multipath fading channels, where no further degradation is caused. This indicates that the proposed method can effectively secure the IMSI of mobile user devices against active and passive attackers by providing a safe network connection between the communicating parties (UE and BS).
Article PDF: https://rs-ojict.pubpub.org/pub/v4kctroh/release/1?readingCollection=cd5de46d
Simulation Code of the paper: https://researcherstore.com/product/simulation-codes-of-a-new-security-design-for-protecting-imsi/
Improve your professional and technical skills at:https://researcherstore.com/courses/





Share this post